 This write-up is from the Token Ring FAQ , by James Messer James@ with quite a few contributions by other people. If the station successfully participates in a ring poll, it proceeds into the final phase of insertion, request initialization. For all Token Ring cards except the CTR and access routers, you must use the clear interface command to reinitialize the Token Ring interface if the interface is down.
This write-up is from the Token Ring FAQ , by James Messer James@ with quite a few contributions by other people. If the station successfully participates in a ring poll, it proceeds into the final phase of insertion, request initialization. For all Token Ring cards except the CTR and access routers, you must use the clear interface command to reinitialize the Token Ring interface if the interface is down.
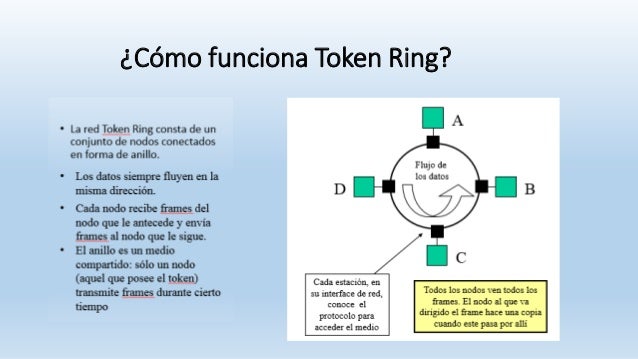
The supply receives the returned token, verifies copied and received information and empties the token. Each Token Ring card comes with a diagnostic disk that supplies testing for the adapter. In Figure Two we can see how Token Ring creates a logical ring network with a physical star.
Below situations of low load, substantial delay waiting for token to come about, even though network is idle. The token is passed around the ring until a pc wishing to send information and … Read the rest >>>>

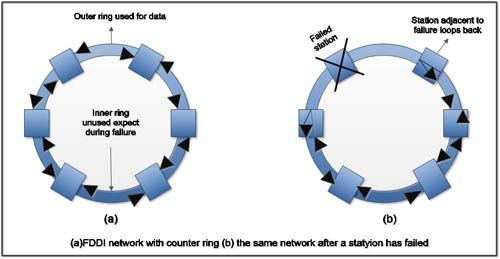
 LAN (Neighborhood Region Network) merupakan jaringan milik pribadi di dalam satu organisasitertentu, gedung atau kampus yang berukuran sampai dengan beberapa kilometer. In a physical Token ring topology, when a cable is open or a station is not operating, the entire network goes down. Token Ring networks employ numerous mechanisms for detecting and compensating for network faults. It started out in 1969 as the Newhall Network, named following the originator of the token ring concept.
LAN (Neighborhood Region Network) merupakan jaringan milik pribadi di dalam satu organisasitertentu, gedung atau kampus yang berukuran sampai dengan beberapa kilometer. In a physical Token ring topology, when a cable is open or a station is not operating, the entire network goes down. Token Ring networks employ numerous mechanisms for detecting and compensating for network faults. It started out in 1969 as the Newhall Network, named following the originator of the token ring concept. Token ring menggunakan twisted pair atau kabel fiber optic, namun dalam perkembangannya teknologi ini jarang digunakan dalam lingkup sekolah2 karena lebih banyak yang memakai Ethernet. A mesh network or mesh topology makes use of separate cable to connect each and every device to just about every other device on the network, giving a straight communication path as shown in the figure below. Yet another type of connecting cable is known as an adapter cable which connects the NIC to the MAU.
Token ring menggunakan twisted pair atau kabel fiber optic, namun dalam perkembangannya teknologi ini jarang digunakan dalam lingkup sekolah2 karena lebih banyak yang memakai Ethernet. A mesh network or mesh topology makes use of separate cable to connect each and every device to just about every other device on the network, giving a straight communication path as shown in the figure below. Yet another type of connecting cable is known as an adapter cable which connects the NIC to the MAU. Adalah sebuah cara akses jaringan berbasis teknologi ring yang pada awalnya dikembangkan dan diusulkan oleh Olaf Soderblum pada tahun 1969. If you keep in mind your network topologies, Token Ring was a ring technologies whereby information went from 1 personal computer to an additional in a ring format. Star topology is made use of in most current information and facts networks that involve data processing and voice communication.
Adalah sebuah cara akses jaringan berbasis teknologi ring yang pada awalnya dikembangkan dan diusulkan oleh Olaf Soderblum pada tahun 1969. If you keep in mind your network topologies, Token Ring was a ring technologies whereby information went from 1 personal computer to an additional in a ring format. Star topology is made use of in most current information and facts networks that involve data processing and voice communication. The most prevalent regional location network option to Ethernet is a network technology created by IBM, known as token ring. When the subsequent token is generated, it consists of the higher priority of the reserving station. One more plus of the Token-Ring strategy is that additional-equal access to the network media is offered when compared to the technique made use of by Ethernet (a device on an Ethernet network can really dominate the network by flooding it with information).
The most prevalent regional location network option to Ethernet is a network technology created by IBM, known as token ring. When the subsequent token is generated, it consists of the higher priority of the reserving station. One more plus of the Token-Ring strategy is that additional-equal access to the network media is offered when compared to the technique made use of by Ethernet (a device on an Ethernet network can really dominate the network by flooding it with information).