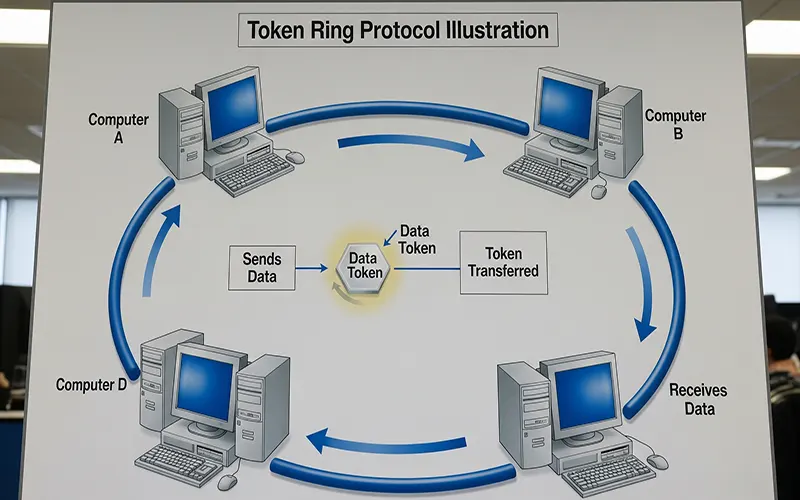
The most prevalent regional location network option to Ethernet is a network technology created by IBM, known as token ring. When the subsequent token is generated, it consists of the higher priority of the reserving station. One more plus of the Token-Ring strategy is that additional-equal access to the network media is offered when compared to the technique made use of by Ethernet (a device on an Ethernet network can really dominate the network by flooding it with information).
Phase 3 (Participation in ring poll) — A station learns the address of its Nearest Active Upstream Neighbour (NAUN) and makes its address recognized to its nearest downstream neighbour, top to the creation of the ring map. If the status line indicates that the interface and line protocol are not up, verify the cable from the router to the MAU.
The initial function is to operate as the master clock for the ring in order to offer synchronization of the signal for stations on the wire. If required, modify ring speed specifications for clientele, servers, and routers. That is grate lesson for students and it helps create our network topology Know-how.
After the token is seized and changed to an details frame, only stations with a priority value greater than that of the transmitting station can reserve the token for the next pass about the network. If you are overriding the burned-in network addresses, it is doable that duplicate node addresses could be set.
It consists of a single cable, identified as a trunk, backbone, or segment, that connects all the computers in the network. Earlier it was pointed out that Token Ring utilizes a token passing Media Access Manage (MAC) protocol. A further function of the AM is to insert a 24-bit delay into the ring, to make certain that there is constantly adequate buffering in the ring for the token to circulate.